As much we all complain about email, for most of us, email is still our primary conduit for online communication. That said, numerous hacks and revelations about government surveillance have made it clear that email is also one of the most vulnerable of those conduits.
What you send via email is your business and yours alone. Besides you and the recipient, no one else should be reading that message. Not hackers, not government agencies, and definitely not nosy siblings or friends.
To ensure that your email stays private, you need to secure it. If you have a degree of technical knowledge and skill, you can set up your own email server that allows you to do that. However, that's not an option for those of us without those skills and that knowledge.
So, what can we do to keep out emails private? Turn to secure, open source email services like the two I cover in this article.
ProtonMail
ProtonMail boasts that it keeps your email messages "encrypted at all times." It does a good job of that. The only time a message isn't encrypted is when it lands in a recipient's inbox.
The service uses several levels of security. When you set up a ProtonMail account, you're encouraged to create two passwords: a login password and a password to decrypt your mailbox. The mailbox password is optional, but if you want an extra layer of security you should set it. You can add even more security to your account using two-factor authentication.
Sending a message to another ProtonMail user automatically encrypts it. When you a message to someone who doesn't use ProtonMail, you can choose to encrypt it. When you do that, you add a password to the message. The recipient gets a link to the message, and enters the password that you set. From there, they can read and reply to the message.
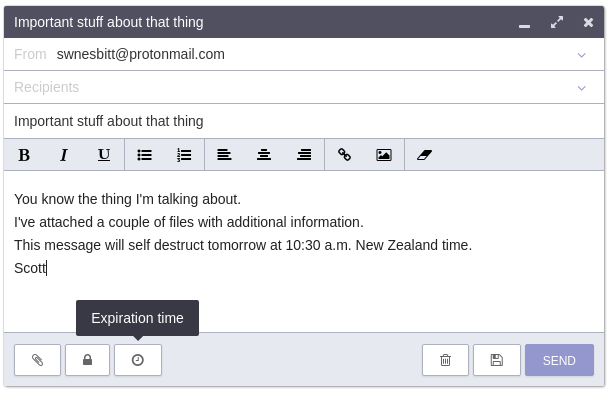
Caption: Composing an email in ProtonMail
You can also set messages to self-destruct after a number of hours, days, or weeks into the future. To do that, you'll also need to set a decryption password for the message. Once the message expires, it becomes digital dust never to be seen again.
ProtonMail is quite easy to use, and its web interface is clean though kind of traditional. You can sign up for a paid account starting at US $4 per month, or peruse the ProtonMail repositories on GitHub.
Tutanota
Tutanota takes a similar approach to protecting your emails. Your inbox is encrypted, and you have the option to either encrypt the message or not. In case you're wondering, messages are end-to-end encrypted if you're sending to someone with a Tutonota email address.
If you do choose to encrypt the message (and why wouldn't you?), you're asked to create a password that the recipient will use to decrypt all emails that you send them. You'll need to securely share that password with them—perhaps via text message, a letter, or a phone call.
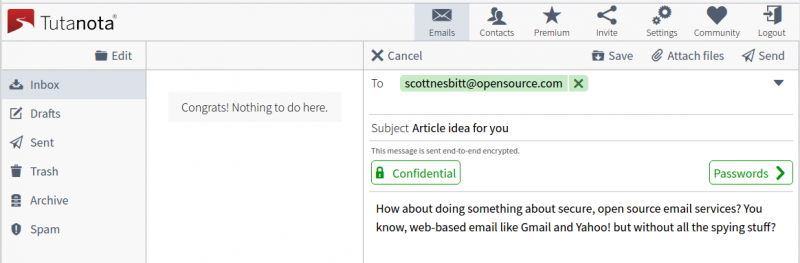
Getting ready to encrypt an email in Tutanota
An email containing the link to the encrypted message lands in the recipient's inbox. They click the link, enter the password, and can read and reply to the message. That all sounds a bit cumbersome, but it's better to be safe than sorry.
Other than that, Tutanota has a very minimal interface and is easy to use. You can also upgrade to a premium account for 12 euros a year. You can learn more about how Tutanota encrypts emails or you can look at the code on GitHub.
Two other options worth noting
You might remember Lavabit as being Edward Snowden's email service of choice. The folks behind Lavabit shut the service down rather than turn over user information to the government. Well, Lavabit is back and it uses a new end-to-end secure communication protocol to protect messages.
If you want to host your own secure email client, then check out Mailpile. It's not a mail server. Instead, Mailpile works with other email services (like Gmail) to encrypt your communication. It uses OpenPGP for encryption, and you can run it on just about any computer, even a Raspberry Pi.
Do you have a favorite secure open source email service? Feel free to tell our community about it by leaving a comment.






8 Comments